how i found a europa.eu compromise (thanks to cricket)
Table of Contents
TLDR
While looking for a way to stream the India vs Pakistan cricket match on 14th September 2025, I stumbled across a suspicious search result on a europa.eu dev subdomain. It was being abused for blackhat SEO and redirecting users to scam streaming sites. I traced similar behavior across other high-profile domains, reported the issue to CERT-EU via email (after some Twitter help) and the problem was later confirmed as fixed on 6th November 2025. This post walks through how I found it, how I reported it and what we can learn from it.
how an India vs Pakistan match led me to a europa.eu compromise⌗
On 14 September 2025, India played Pakistan in one of those absolutely wild, high-stakes cricket matches.
If you are from India or Pakistan, you already know: this is not just a “match”. It is a festival.
people take leave from work
entire days are planned around the game
The celebrations are huge.
What I did not expect was that this festival would somehow lead me to a compromised europa.eu dev server.
India vs Pakistan -> europa.eu compromise.
Yeah, I was also confused.
looking for a stream… and finding europe instead⌗
I searching for which OTT services is aurtorised for “India vs Pakistan live”.
That’s when a very strange search result showed up:
a **europa.eu** link
promising guidance on *how to watch the India vs Pakistan match live*
That alone set off my blue-teamer brain.
Why is an EU domain telling me how to stream a cricket match between India and Pakistan?
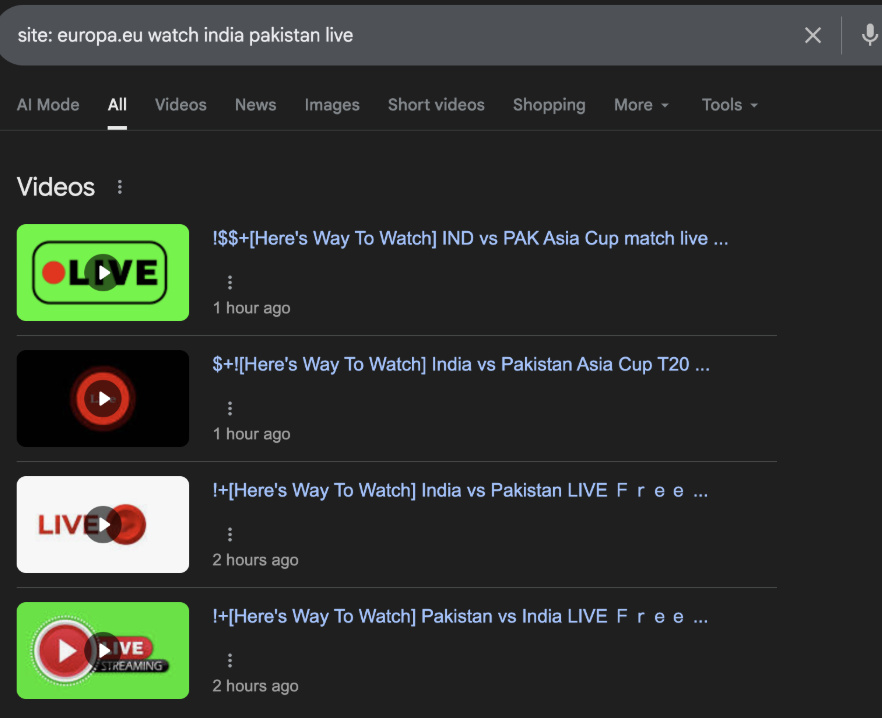
Suspicious search result from a europa.eu domain claiming to help stream the match.
I clicked the link (safely, in a controlled environment) and instead of any EU content, it redirected me to a random scammy streaming site.
At this point one thing was clear:
this looked exactly like SEO poisoning using a trusted domain (in this case europa.eu) to funnel users into suspicious streaming sites.
the dev server behind it: openapi-dev.ema.europa.eu⌗
On closer inspection of the URL, I noticed this was the impacted host:
hxxps://openapi-dev.ema.europa[.]eu/
A dev server.
Exposed to the internet.
Being used for blackhat SEO-related redirects.
That combination alone is already a red flag.
When I tried visiting some of the URLs I had captured from search results, I observed:
sometimes I’d hit 404 or 500
sometimes I’d get redirected to a random streaming scam site
the content and target URLs appeared to change over time
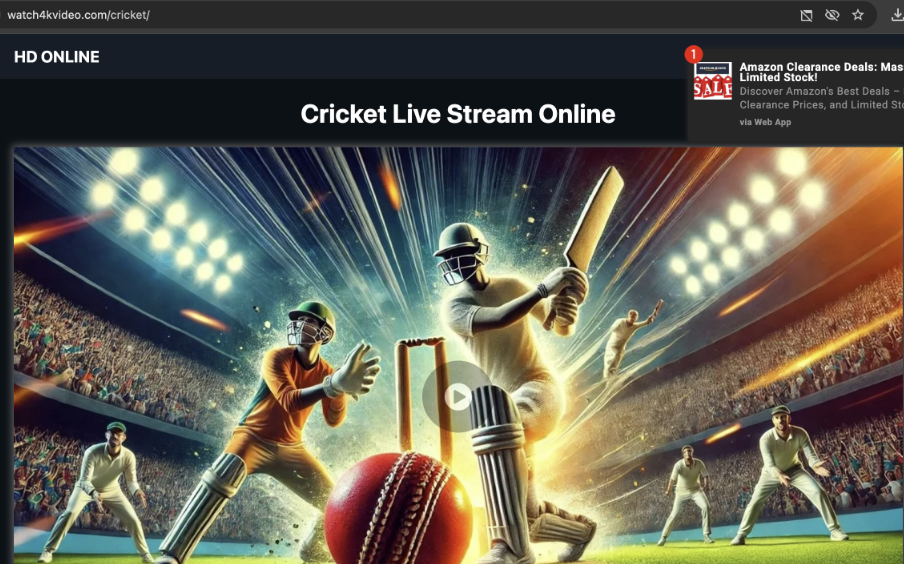
Caption: Example of a scam streaming site reached after redirection.
This rotating behavior is pretty typical for SEO spam / poisoning campaigns. Payloads and keywords change over time to ride whatever is trending.
At this point I thought:
okay, this probably needs to be reported to the relevant CERT but I am not sure which contact is correct.
So I did the most natural 2025 move.
I tweeted.
twitter, friends and finding the right cert contact⌗
I first put my observation on X (Twitter) to document it and to see if anyone could guide me on the right reporting channel:
- Tweet 1 (initial finding):
https://x.com/anand_himanshu/status/1967325757602136238

Caption: First tweet where I shared the suspicious europa.eu behavior.
There was no immediate response from any official EU account. So I followed up and tagged a few security folks who I knew might have better visibility or contacts.
- Tweet 2 (asking for help):
https://x.com/anand_himanshu/status/1967571763929473520

Caption: Follow-up tweet tagging friends from the security community.
Special thanks to:
- @UK_Daniel_Card
- @zachxbt
- @mylaocoon
- @vxunderground
They helped point me towards the right CERT-EU contact email.
Pro tip from this whole thing:
even for big organizations, having a clear security.txt or disclosure page makes everyone’s life easier.
emailing cert-eu: “Security Incident - Infected Subdomain (openapi-dev.ema.europa.eu)”⌗
Armed with the correct email, I finally reached out to:
I shared:
the suspicious URLs
the behavior I observed (redirects to scam streaming sites)
context that this looked like **SEO poisoning** on a dev host of europa.eu
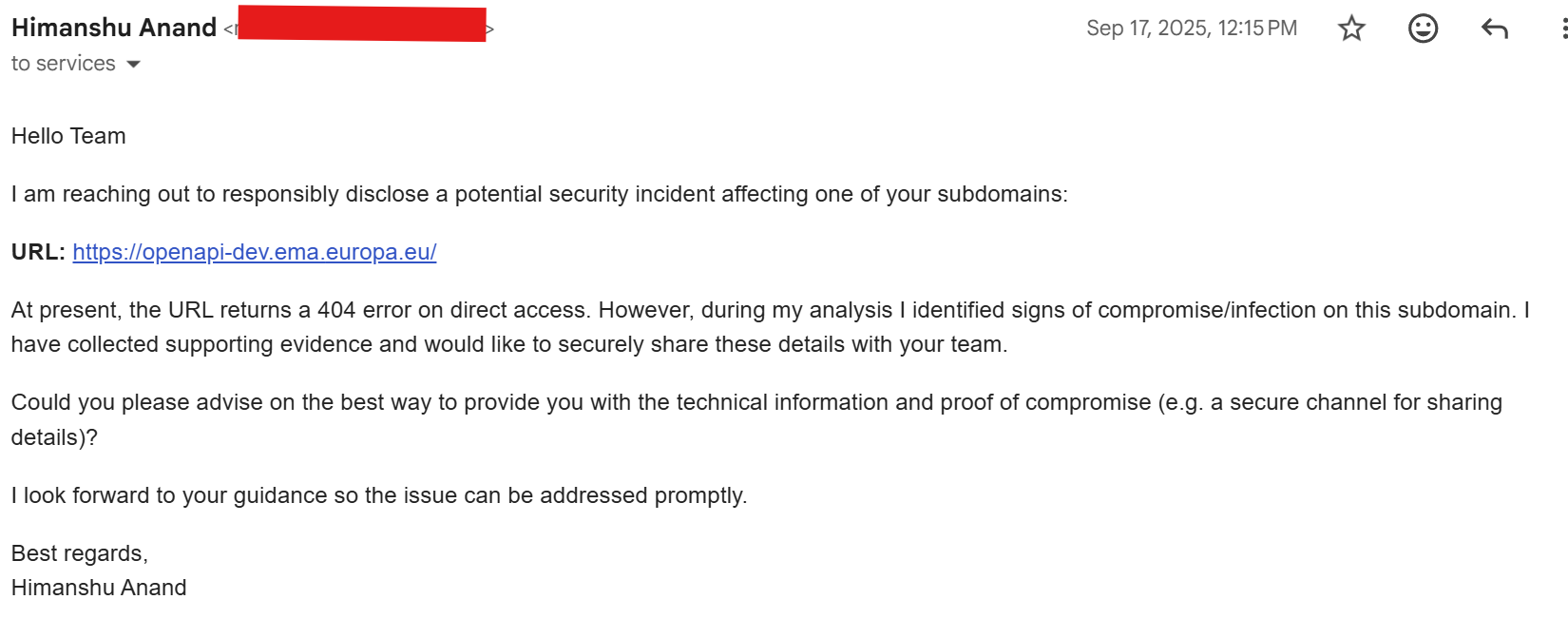
Caption: Initial email to CERT-EU describing the behavior.
They replied but they were unable to reproduce the issue right away:
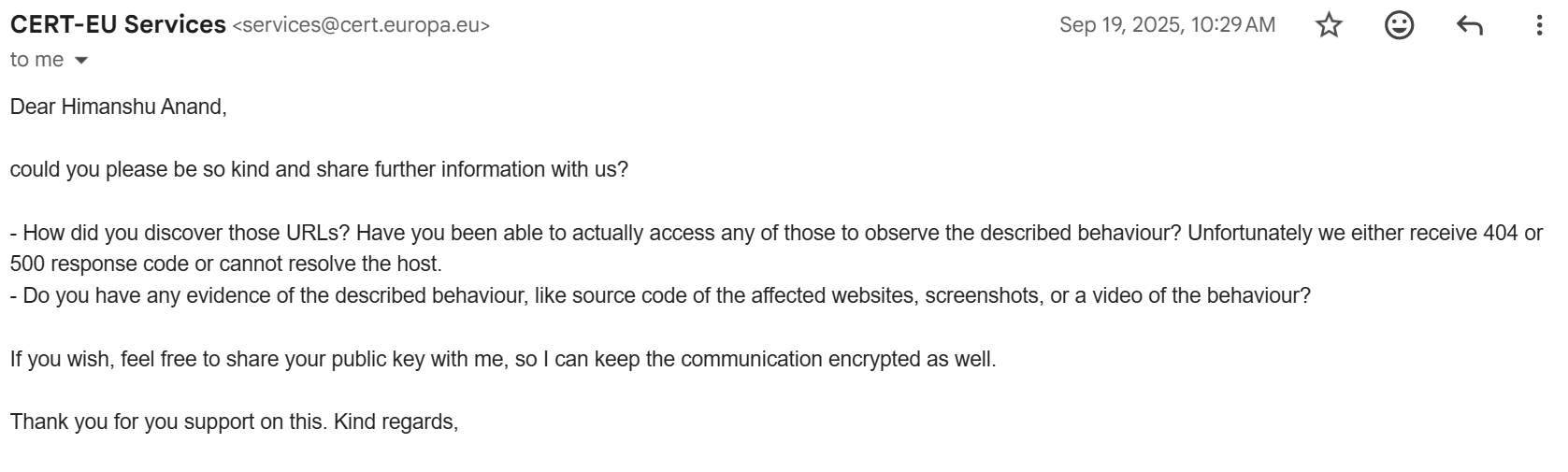
Caption: CERT-EU asking for details and reproducible evidence.
This is where the rotating / inconsistent behavior of SEO campaigns becomes annoying: by the time defenders go to check, the payload might already have moved, rotated or partially broken.
I shared more screenshots and context to help them see what I had observed.
this looked a lot like 360xss-style mass seo poisoning⌗
While doing my analysis, I remembered a great writeup that described mass SEO exploitation via a virtual tour framework:
- 360XSS: Mass Website Exploitation via Virtual Tour Framework for SEO Poisoning
https://olegzay.com/360xss/
I won’t claim this was exactly the same attack but the TTPs were very similar:
abuse of legitimate, high-trust domains
modified SEO content / titles like "[Here's Way To Watch]"
redirection chains leading to streaming scam or spam sites
behavior changing over time as campaigns rotate
At minimum, it looked like the same family of problems: compromised pages being weaponized not to drop malware but to hijack SEO for traffic.
europa.eu was not alone: more big sites in the same campaign⌗
While digging deeper and using the same patterns and dorks, I realized this wasn’t just an EU issue.
I also observed similar behavior on other high-profile domains, including:
https://www.isb.companiesoffice.govt.nz/
https://nal.usda.gov
https://ampl.clair.ucsb.edu/
And if you want to explore this yourself here is one very telling Google dork:
intitle:"[Here's Way To Watch]"
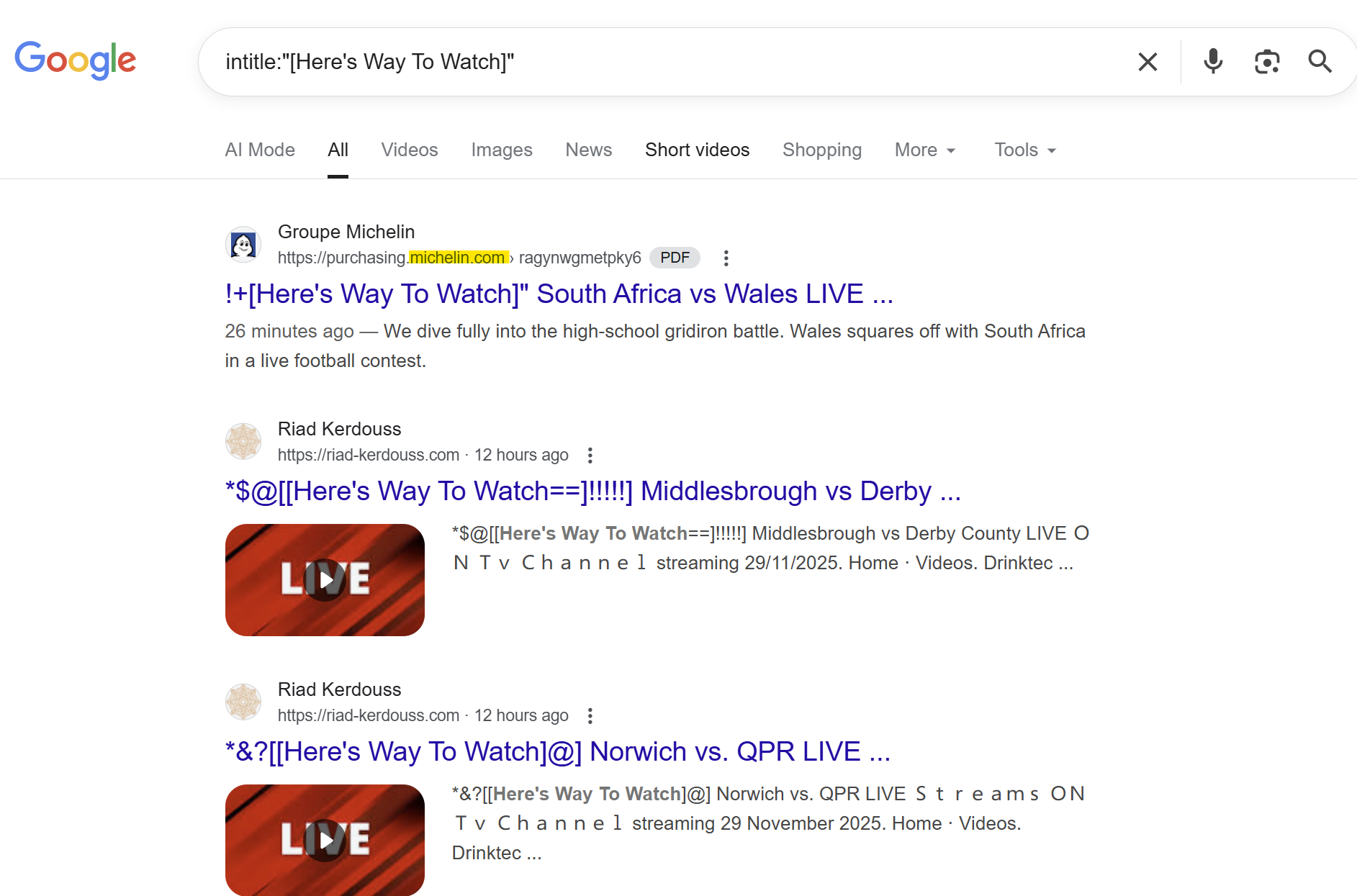
Caption: Google dork results showing multiple sites with the same SEO payload pattern.
One of the more notable hits was michelin.com, which pretty much confirms that attackers had gone for breadth, not just niche or small domains.

Caption: Meme-worthy moment: when you just wanted to watch cricket and end up mapping an SEO spam campaign across major domains.
not hall-of-fame material, but still important⌗
At some point in the exchange, CERT-EU clarified that:
they could not treat this as a vulnerability report eligible for Hall of Fame publication.
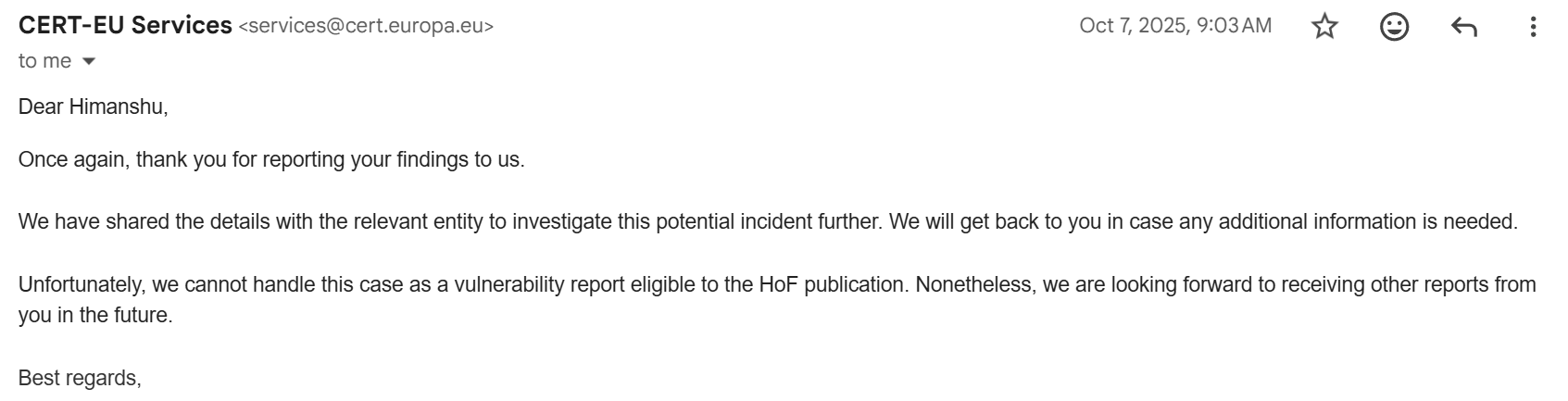
Caption: CERT-EU confirming the case is not HoF-eligible.
Honestly, that’s fair. This was not a critical RCE or some zero-day that could bring the EU offline.
But it does highlight a funny reality of security:
- Hack one site and brag -> hero status.
- Quietly report that a big domain is being abused -> often nobody notices.
Still worth doing it every time.
timeline: from cricket match to fix⌗
Here is the rough sequence of events:
**14 September 2025** : India vs Pakistan match; I spot suspicious *europa.eu* search result related to streaming.
**Mid-September 2025** : I analyze the behavior, identify `openapi-dev.ema.europa.eu` as impacted, find similar issues on other domains, and tweet about it.
**17 September 2025** (approx.) : I send my first email to CERT-EU at `[email protected]`.
**Following days** : We exchange emails; they initially cannot reproduce the issue and ask for more details.
**6 November 2025** : CERT-EU informs me that the issue has been fixed.
**29 November 2025** : I finally publish this blog post.
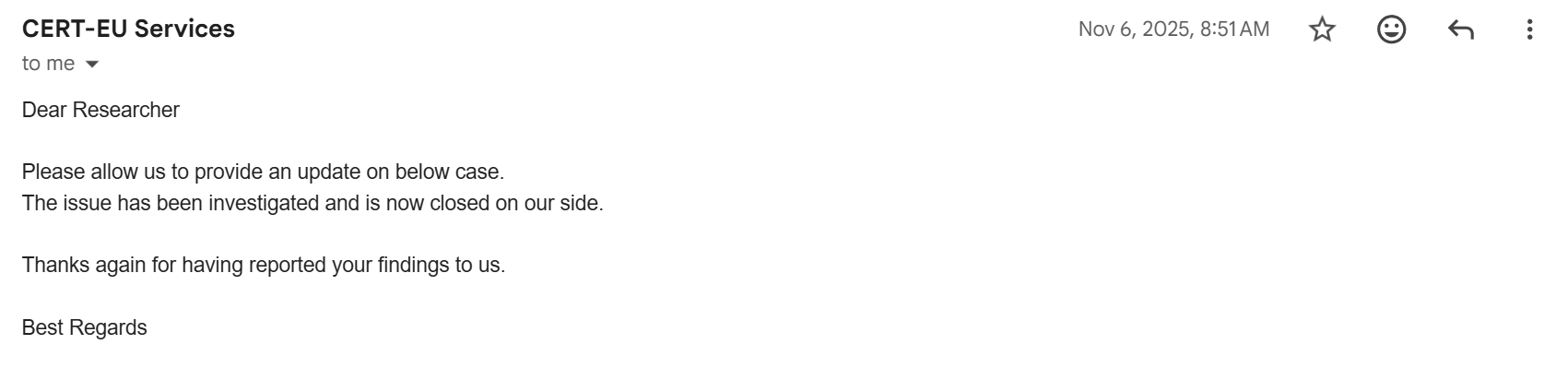
Caption: CERT-EU confirming the issue has been fixed on their side.
I also asked whether they could share anything from an incident response perspective for the community and whether they were okay with me blogging this. I have not seen a detailed IR writeup yet but I have given this a reasonable amount of time before publishing.
what probably happened (my educated guess)⌗
This section is my hypothesis not an official statement from CERT-EU.
Based on what I observed and what we know about similar campaigns:
-
A dev server was exposed to the internet
openapi-dev.ema.europa.euwas reachable publicly when it probably shouldn’t have been.
-
Attackers found a way to inject or modify SEO-relevant content
- This might have been a stored XSS, misconfigured template or some CMS/plugin endpoint.
- The goal was not to deface the site, but to hijack search engine results.
-
They rotated keywords based on trending topics
- Big matches like India vs Pakistan are perfect bait.
- Titles like
"[Here's Way To Watch]"strongly suggest SEO-driven campaigns.
-
The redirection targeted scam streaming pages
- Once users clicked the search result, they would end up on random streaming or scam sites.
- This is great traffic for shady affiliates, subscription scams or ad fraud.
-
Deeper compromise (like webshells or long-term RCE) feels unlikely
- If they had long-term, reliable RCE on high-profile domains, using them only for SEO spam would be a waste.
- SEO campaigns benefit more from wide, shallow compromise than from deep, single target persistence.
-
The server was likely taken offline or cleaned as part of IR
- Given that CERT-EU confirmed the issue is fixed, it is safe to assume:
- exposure was removed and/or
- malicious content was removed and
- underlying misconfigurations were corrected.
- Given that CERT-EU confirmed the issue is fixed, it is safe to assume:
what we can learn from this⌗
A few takeaway points for defenders, blue-teamers and anyone running public-facing infrastructure:
1. even dev servers matter⌗
Just because it is a “dev” host does not mean it won’t be:
indexed by search engines
abused by attackers
trusted by users (or at least by Google’s ranking)
If a dev subdomain lives under a high-trust parent like europa.eu, it inherits a lot of credibility.
2. seo poisoning is not “harmless” noise⌗
It’s easy to ignore SEO spam as “just” nuisance. But it:
manipulates users into scam flows
abuses brand trust
can be a signal of deeper weaknesses (XSS, misconfig, outdated apps)
Even if the worst case here isn’t data exfiltration, it’s still worth fixing.
3. security.txt (or equivalent) helps a lot⌗
The fact I had to go via Twitter and friends to find the right reporting contact is… not ideal.
A simple well-maintained security.txt or even a clear “Report a vulnerability” page can:
- reduce the time from discovery to report
- avoid reports getting lost in generic inboxes
- encourage more people to report issues responsibly
4. sharing IR details (when possible) benefits everyone⌗
I fully understand not every incident can be disclosed in detail.
But where possible, sharing even a sanitized, high-level IR summary is incredibly helpful:
helps other orgs recognize similar patterns
raises awareness of specific campaigns
improves collective defense against things like mass SEO poisoning
5. if something looks off, report it⌗
This all started because:
I searched for an India vs Pakistan stream
saw a suspicious *europa.eu* result
and did not just scroll past
You don’t need a zero-day to be helpful.
If you notice weird redirects, unexpected search results or strange behavior on big domains:
take screenshots
collect URLs
and report it to the right CERT / security contact.
Worst case: it’s nothing.
Best case: you help someone clean up a compromise.
closing thoughts⌗
This was not a nation-state APT or a dramatic multi-stage intrusion with custom malware.
It was something quieter:
a **dev subdomain** of `europa.eu` being abused for **blackhat SEO**
part of a broader campaign affecting multiple large, trusted domains
discovered by accident while I just wanted to watch some cricket
But these smaller things matter too.
They erode trust slowly. They teach attackers that abusing big brands for SEO spam is easy and low-risk. And they serve as gentle reminders that even very mature organizations can still have dev subdomains exposed in ways they did not expect.
If you work in defense:
keep an eye on what search engines see for your domains
regularly review exposed dev/staging hosts
and don’t underestimate "weird SEO" as an early signal
And if you’re just here for the story:
yes, a cricket match did indirectly help clean up a europa.eu dev server
no, I did not actually "save the EU"
but I will absolutely joke about it anyway 😄
stay curious, stay safe and maybe next time your match-day Google search will uncover something interesting too.